OpenVPN
Updated 7 February 2023
OpenVPN is a free implementation of the open source virtual private network (VPN) technology that aims at creating encrypted point-to-point or server-to-client channels between hosts. It allows you to establish connections between computers behind NAT and the firewall without changing their settings.
Important
Note that, for correct operation, the time on all computers must be the same.
Creating PKI certificates for OpenVPN
Package installation and setup
Install the necessary software:
emerge easy-rsa
Once the package installed, a directory called /usr/share/easy-rsa will be created, containing the easyrsa script to work with certificates. Keys and certificates will be stored there too. Move it to /var/calculate/easy-rsa and then go to this directory to continue:
cp -a /usr/share/easy-rsa /var/calculate
cd /var/calculate/easy-rsa
tree
. ├── easyrsa ├── openssl-1.0.cnf ├── vars.example └── x509-types ├── ca ├── client ├── COMMON └── server 1 directory, 7 files
Configure the certificate. To do so, first copy the sample file:
cp vars.example vars
Edit if necessary:
vars
set_var EASYRSA_REQ_COUNTRY "GB" set_var EASYRSA_REQ_CITY "London" set_var EASYRSA_REQ_ORG "My Company" set_var EASYRSA_REQ_EMAIL "my@domain.org" ...
Create a certificate tree:
Note: using Easy-RSA configuration from: ./vars init-pki complete; you may now create a CA or requests. Your newly created PKI dir is: /var/calculate/easy-rsa/pki
Once completed, a directory called /var/calculate/easy-rsa/pki will be created for keys and certificates storage.
tree
. ├── easyrsa ├── openssl-1.0.cnf ├── pki │ ├── private │ └── reqs ├── vars ├── vars.example └── x509-types ├── ca ├── client ├── COMMON └── server 4 directories, 8 files
Root certificate
Create a root certificate. Enter you password twice and specify the certificate name:
Note: using Easy-RSA configuration from: /var/calculate/easy-rsa/vars Generating a 2048 bit RSA private key ....................................................+++ ......................................................................................................+++ writing new private key to '/var/calculate/easy-rsa/pki/private/ca.key.w3cG6vF0cv' Enter PEM pass phrase: Verifying - Enter PEM pass phrase: ----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Common Name (eg: your user, host, or server name) [Easy-RSA CA]:domain.org CA creation complete and you may now import and sign cert requests. Your new CA certificate file for publishing is at: /var/calculate/easy-rsa/pki/ca.crt
Replace domain.org with a certificate name of your choice or specify your domain.
tree pki
pki ├── ca.crt ├── certs_by_serial ├── index.txt ├── issued ├── private │ └── ca.key ├── reqs └── serial 4 directories, 4 files
Were therefore created:
- ./pki/ca.crt , a root CA certificate
- ./pki/private/ca.key , a private key of the root CA (which is the most important file)
Server certificate
Create a certificate for the OpenVPN server. To do this, run the following:
Note: using Easy-RSA configuration from: ./vars
Generating a 2048 bit RSA private key
.......+++
.......................+++
writing new private key to '/var/calculate/easy-rsa/pki/private/server.key.mfeee1imNK'
-----
Using configuration from /var/calculate/easy-rsa/openssl-1.0.cnf
Enter pass phrase for /var/calculate/easy-rsa/pki/private/ca.key:
Check that the request matches the signature
Signature ok
The Subject's Distinguished Name is as follows
commonName :ASN.1 12:'server'
Certificate is to be certified until Feb 20 20:00:53 2028 GMT (3650 days)
Write out database with 1 new entries
Data Base Updated
You will be prompted for a root certificate password. Replace server with your server certificate. By default, a certificate is valid 10 years.
Once the script has been completed, the following files are created:
- ./pki/issued/server.crt which is a server certificate,
- ./pki/private/server.key which is the server private key.
Client certificate
Create a certificate for the client similar the server OpenVPN certificate. To do this, run the following:
Note: using Easy-RSA configuration from: ./vars
Generating a 2048 bit RSA private key
..................................................+++
................................................................................+++
writing new private key to '/var/calculate/easy-rsa/pki/private/client.key.qfTovtcVDo'
-----
Using configuration from /var/calculate/easy-rsa/openssl-1.0.cnf
Enter pass phrase for /var/calculate/easy-rsa/pki/private/ca.key:
Check that the request matches the signature
Signature ok
The Subject's Distinguished Name is as follows
commonName :ASN.1 12:'client'
Certificate is to be certified until Feb 20 20:34:40 2028 GMT (3650 days)
Write out database with 1 new entries
Data Base Updated
You will be prompted for a root certificate password. Replace client with your client certificate. By default, this certificate is also valid 10 years.
Once the script has been completed, the following files are created:
- ./pki/issued/client.crt is the client certificate
- ./pki/private/client.key is the private key
Diffie-Hellman key
To create a Diffie-Hellman key, run:
Note: using Easy-RSA configuration from: ./vars Generating DH parameters, 2048 bit long safe prime, generator 2 This is going to take a long time ... DH parameters of size 2048 created at /var/calculate/easy-rsa/pki/dh.pem
A file containing the ./pki/dh.pem key will be created.
An additional secret key
Create an additional key for more protection:
openvpn --genkey --secret pki/ta.key
A file containing the ./pki/ta.key key will be created.
Server configuration
Installation
First install OpenVPN:
emerge openvpn
Getting keys and certificates
Create a directory where the certificates will be stored:
mkdir /etc/openvpn/keys
Copy the PKI keys and certificates you created. If the OpenVPN server is located on the same computer, run the following:
cp /var/calculate/easy-rsa/pki/ca.crt /etc/openvpn/keys/
cp /var/calculate/easy-rsa/pki/dh.pem /etc/openvpn/keys/
cp /var/calculate/easy-rsa/pki/issued/server.crt /etc/openvpn/keys/
cp /var/calculate/easy-rsa/pki/private/server.key /etc/openvpn/keys/
cp /var/calculate/easy-rsa/pki/ta.key /etc/openvpn/keys/
Server configuration
Edit the OpenVPN configuration file as shown below:
/etc/openvpn/openvpn.conf
# port, protocol, device, compression method port 1194 proto udp dev tun allow-compression no # keys and certificates ca keys/ca.crt cert keys/server.crt key keys/server.key dh keys/dh.pem tls-auth keys/ta.key 0 # allocated IP range, default route, DNS server 192.168.10.0 255.255.255.0 # network topology topology subnet push "redirect-gateway def1" push "dhcp-option DNS 8.8.8.8" # restart tunnel if necessary keepalive 10 120 # openvpn privileges user openvpn group openvpn # keep device and key files unchanged when restarting the tunnel persist-tun persist-key # info on current connections status /var/log/openvpn-status.log
When using +redirect-gateway OpenVPN clients will send DNS requests via VPN, and the VPN server must know how to handle them. This can be achieved by passing the address of the DNS server to the connecting clients, thus replacing their regular DNS settings as long as VPN remains active. In the example above, this is handled by push "dhcp-option DNS 8.8.8.8", where 8.8.8.8 is the Google DNS address.
Important
Many hosts connected to the Internet via an OpenVPN client will periodically interact with the DHCP server to resume their IP lease. The redirect-gateway option may prevent the client from contacting the local DHCP server (as DHCP messages will be routed via VPN), resulting in loss of lease.
Restart the server and add it to the autostart:
/etc/init.d/openvpn start
rc-update add openvpn
Forwarding configuration
Enable packet forwarding between network interfaces:
/etc/sysctl.conf
net.ipv4.ip_forward = 1
To apply, run:
sysctl -p /etc/sysctl.conf
Forwarding redirect-gateway to the client will force all IP traffic generated on the client machine to pass through the OpenVPN server. The server must be configured to handle this traffic, for forwarding it via NAT, for example. To route the client's traffic via NAT, run:
iptables -t nat -A POSTROUTING -s 192.168.10.0/24 -o eth0 -j MASQUERADE
Replace eth0 with the local network interface of the server.
Save the routing rules and add them to autostart:
/etc/init.d/iptables save
rc-update add iptables
Client configuration
Installation
Install a client for OpenVPN:
emerge openvpn
Getting keys and certificates
Create a directory where the certificates will be stored:
mkdir /etc/openvpn/keys
Copy the PKI keys and certificates you created. If the OpenVPN server is located on the host where the keys were created, run:
cp /var/calculate/easy-rsa/pki/ca.crt /etc/openvpn/keys/
cp /var/calculate/easy-rsa/pki/issued/client.crt /etc/openvpn/keys/
cp /var/calculate/easy-rsa/pki/private/client.key /etc/openvpn/keys/
cp /var/calculate/easy-rsa/pki/ta.key /etc/openvpn/keys/
Client configuration
Edit the client configuration file, as shown below:
/etc/openvpn/openvpn.conf
client
# protocol, device, compression method
proto udp
dev tun
allow-compression no
# remote server, port
remote vpn.domain.org 1194
# keep device and key files unchanged when restarting the tunnel
persist-tun
persist-key
remote-cert-tls server
# keys and certificates
ca keys/ca.crt
cert keys/client.crt
key keys/client.key
tls-auth keys/ta.key 1
# log
status /var/log/openvpn-status.log
Replace vpn.domain.org with the network name of your VPN server.
Client configuration over a OVPN profile
Getting a profile file
To connect some OpenVPN clients, you may have to use the configuration profile.
That is even better, as you do not have to enter or transfer certificates and keys. Simply create a ovpn file, containing your configuration profile.
This file has the following structure: first the settings of the OpenVPN client are described, then come, in tags, the root certificate, the security key, the client's certificate and the client's key. To do so, follow the procedure described below. Create an ovpn client file and fill it with the following:
client.ovpn
client
proto udp
dev tun
allow-compression no
remote vpn.domain.org 1194
persist-tun
persist-key
key-direction 1
remote-cert-tls server
Replace vpn.domain.org with the network name of your VPN server or its IP address.
Then move all necessary keys and certificates to the profile file. Put tags around:
echo '<ca>' >> client.ovpn cat /var/calculate/easy-rsa/pki/ca.crt >> client.ovpn echo '</ca>' >> client.ovpn echo '<cert>' >> client.ovpn cat /var/calculate/easy-rsa/pki/issued/client.crt >> client.ovpn echo '</cert>' >> client.ovpn echo '<key>' >> client.ovpn cat /var/calculate/easy-rsa/pki/private/client.key >> client.ovpn echo '</key>' >> client.ovpn echo '<tls-auth>' >> client.ovpn cat /var/calculate/easy-rsa/pki/ta.key >> client.ovpn echo '</tls-auth>' >> client.ovpn
Installing and configuring the client
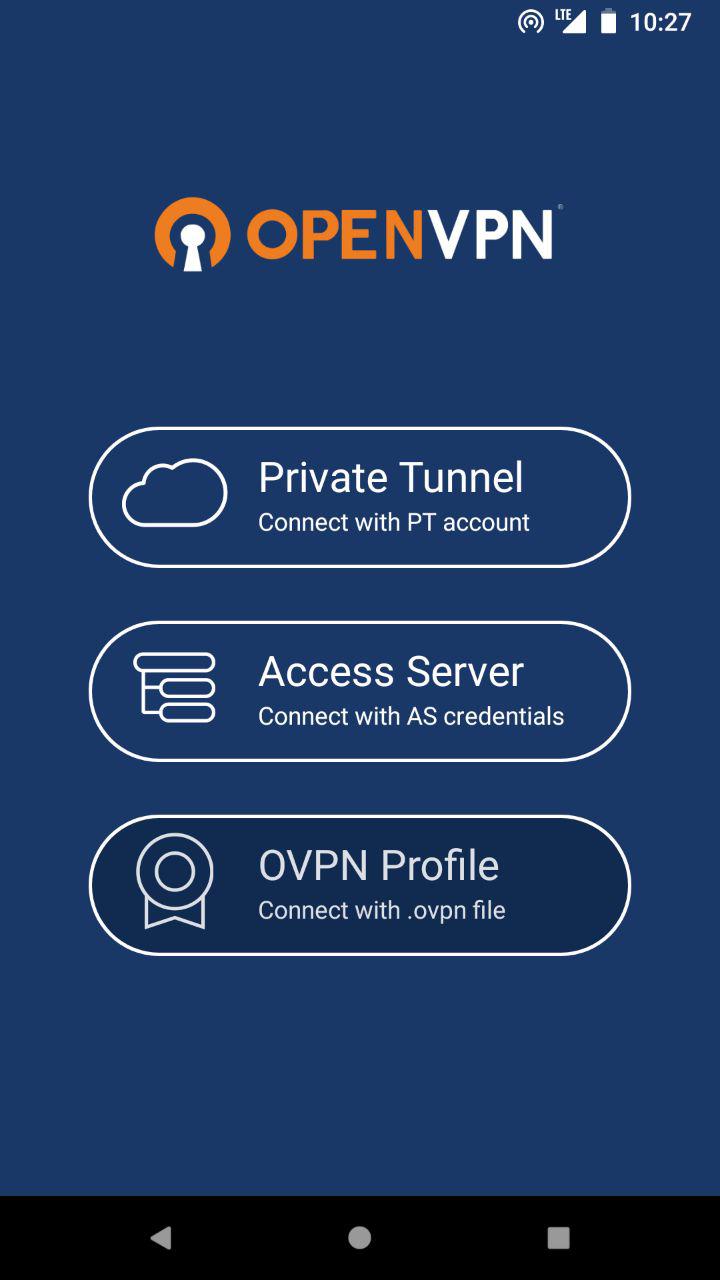
There are several OpenVPN clients for Android. The most popular ones are OpenVPN for Android, OpenVPN Connect and OpenVPN Settings. The latter needs root access rights.
To connect an Android OpenVPN client, download your profile file on your mobile device (with Google Drive or any similar service). Now open your OpenVPN client and select OVPN Profile: